Quick answer
Local business directory submission in Washington works best when teams run an explicit route model instead of one generic statewide workflow. The state has different operating patterns across routes, so quality control should be route-specific even when governance remains centralized.
A practical Washington execution sequence:
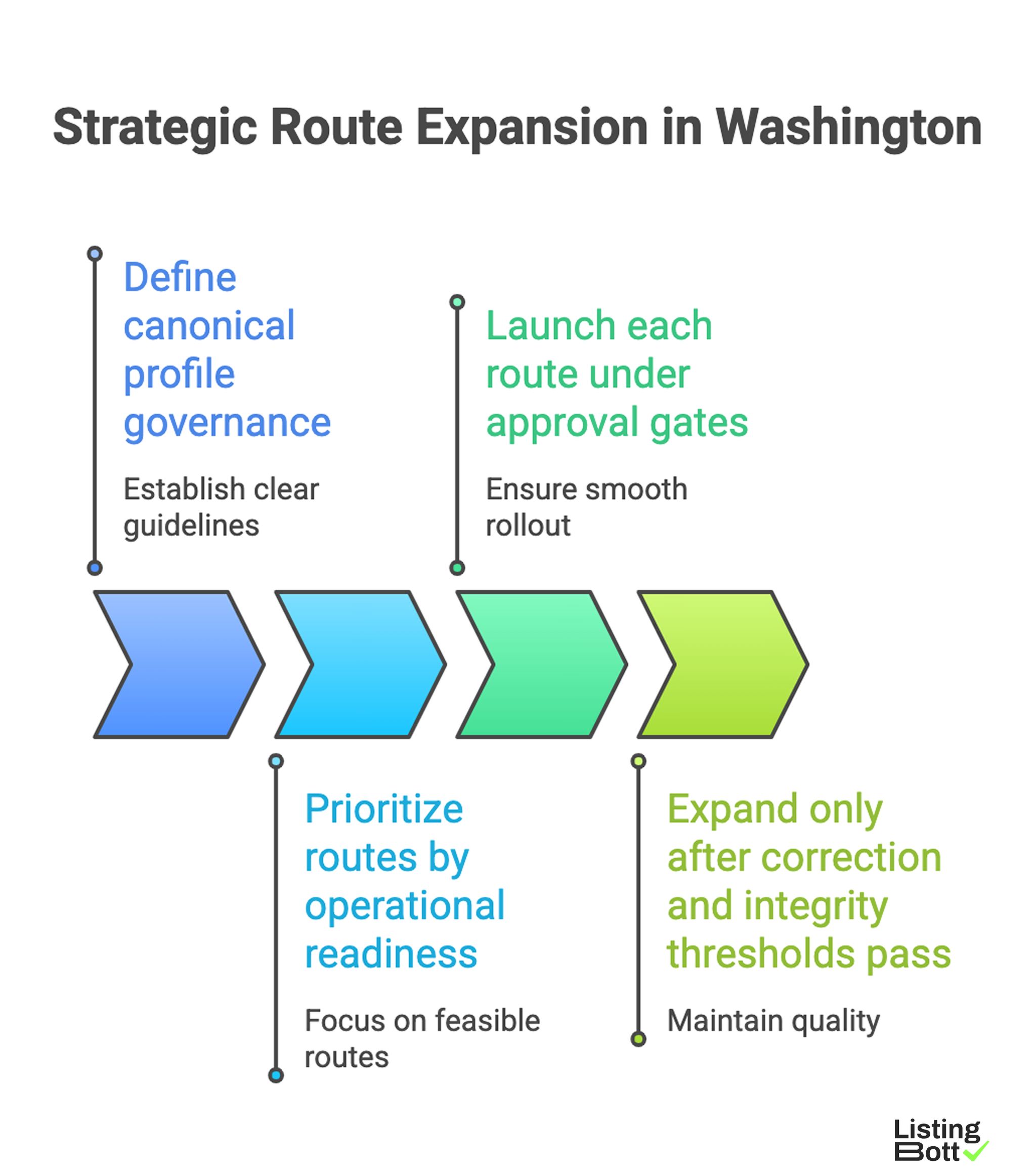
Strategic Route Expansion in Washington
- define canonical profile governance,
- prioritize routes by operational readiness,
- launch each route under approval gates,
- expand only after correction and integrity thresholds pass.
For broader U.S. planning, see Local business directory submission USA.
sbb-itb-8e44301
Methodology
This page uses a route-oriented operating system for Washington. The goal is to make expansion decisions based on route quality, not submission volume.
The MAPS framework (Mapping, Assurance, Prioritization, Stabilization)
| Framework pillar | Weight | Operational question |
|---|---|---|
| Mapping precision | 25 | Are market differences represented in route design? |
| Assurance discipline | 30 | Are quality controls preventing bad data from scaling? |
| Prioritization logic | 20 | Are highest-value routes launched first with control? |
| Stabilization speed | 25 | Can corrections close quickly enough before expansion? |
Scoring method:
- score each pillar from 1-5,
- calculate weighted readiness score,
-
expansion allowed only when score is
>=3.6and no critical KPI is failing.
Washington route taxonomy
| Route type | Example operating pattern | Main objective | Early-warning signal |
|---|---|---|---|
| High-intensity route | high submission frequency and fast data changes | keep quality stable under pressure | rising critical issue age |
| Transition route | mixed density and mixed ownership | transfer baseline controls without drift | inconsistent source fields |
| Distributed route | lower density, broad geography | maintain cadence and reporting clarity | delayed status updates |
| Long-tail route | many low-volume local segments | expand efficiently without quality debt | hidden backlog growth |
Route readiness scoring rubric
| Dimension | Score 1 | Score 3 | Score 5 |
|---|---|---|---|
| Data baseline maturity | no single source of truth | canonical standard defined but not fully enforced | fully enforced baseline with audit trail |
| Owner accountability | no clear owner by route | owner defined but escalation path incomplete | owner + escalation policy active |
| Correction throughput | backlog growing, no SLA adherence | mixed SLA adherence, trend unstable | SLA adherence stable, backlog controlled |
| Reporting reliability | global totals only | partial route segmentation | full route-level visibility and trend history |
| Expansion governance | calendar-driven expansion | mixed threshold/calendar decisions | threshold-driven expansion only |
Use this rubric before opening each new route wave. If any dimension scores 1, hold expansion regardless of total score.
Approval-gate protocol for route launches
| Gate | Decision point | Required artifact | Hard-stop condition |
|---|---|---|---|
| Gate A: baseline sign-off | before first route launch | canonical profile spec + source owner table | conflicting profile baselines |
| Gate B: route scope sign-off | before each wave | approved inclusion/exclusion list | unapproved scope change |
| Gate C: quality review | after first route batch | route integrity report + issue classification | critical issue threshold exceeded |
| Gate D: expansion review | before next route | readiness score and SLA trend | unresolved critical backlog |
Incident classification system (route operations)
| Incident class | Definition | Typical action | Target closure |
|---|---|---|---|
| Class 1 | formatting inconsistency without downstream risk | batched correction cycle | same review cycle |
| Class 2 | repeated profile mismatch in active route | focused correction sprint | within weekly SLA |
| Class 3 | systemic route integrity failure | expansion freeze + root-cause review | before any new route launch |
A clear incident system prevents small quality issues from becoming structural rollout failures.
90-day Washington execution map
| Phase | Window | What happens | Exit criteria |
|---|---|---|---|
| Governance setup | Days 1-15 | baseline policy, role map, gate definitions | governance package approved |
| Controlled route launch | Days 16-38 | launch first route and instrument quality metrics | stable integrity + correction trend |
| Stabilization sprint | Days 39-60 | reduce issue age and improve closure velocity | class 2/3 incidents under control |
| Expansion wave | Days 61-90 | add next routes under same gate system | no KPI regression after expansion |
Practical route launch checklist
| Checklist item | Validation test | Pass standard |
|---|---|---|
| Canonical source enforcement | all route owners use same approved profile source | 100% compliance in audit sample |
| Scope lock before publish | route list approved before execution starts | no post-launch scope edits without gate sign-off |
| SLA configuration | critical issues have defined response/closure targets | SLA breaches tracked and reviewed |
| Route reporting dashboard | route-level quality and backlog visible weekly | trendline available for each route |
| Expansion stop rule | next route blocked on KPI thresholds | expansion frozen automatically when thresholds fail |
Comparison table
| Operating model | Best for | What it does well | Main weakness | Washington fit |
|---|---|---|---|---|
| Single workflow statewide | small test programs only | easy to start | poor resilience across route variance | Low |
| Manual regional operations | limited-scope internal teams | flexible local adjustments | low repeatability and high coordination cost | Medium-low |
| Managed route execution | teams prioritizing fast but controlled rollout | consistent execution with less internal overhead | requires transparent process handoff | Strong |
| Hybrid governance + execution | teams with internal QA leadership | best balance of speed and control | requires strict role boundaries | Very strong |
Decision matrix by team profile
| Team profile | Recommended approach | Why |
|---|---|---|
| Early-stage team with limited ops | Managed route execution | reduces complexity while preserving governance |
| Growth-stage team with active QA owner | Hybrid model | combines external throughput with internal control |
| Mature operations team | Hybrid or internal software-led | supports high-control execution at scale |
| Team with recurring quality debt | Managed pilot + reset | restores baseline before broad expansion |
KPI set to run weekly
| KPI | What it reveals | Trigger to hold expansion |
|---|---|---|
| Route integrity pass rate | data quality stability by route | sustained decline in active route |
| Critical issue age | correction responsiveness | unresolved critical items past SLA |
| Reopen rate | correction quality after closure | rising reopen trend |
| Backlog pressure score | operational debt accumulation | continuous week-over-week increase |
| BOFU progression actions | commercial impact alignment | informational engagement without progression |
Best by use case
1) Single-location operator
Best fit: managed execution with clear route status visibility.
Reason: this minimizes operational burden while preserving quality controls.
2) Multi-location brand operating across Washington
Best fit: hybrid governance with route-by-route expansion gates.
Reason: scaling stays controlled while route-level accountability remains clear.
3) Product-led SaaS team targeting local discovery
Best fit: phased route rollout tied to readiness thresholds.
Reason: threshold-based expansion avoids unstable scale.
4) Agency managing multiple client programs
Best fit: standardized route workflow with formal escalation protocol.
Reason: agencies need repeatable delivery and predictable risk controls.
5) Compliance-heavy organizations
Best fit: approval-first route operations with documented gate artifacts.
Reason: traceable gate decisions reduce policy variance and review risk.
For benchmark references when comparing options, review best directory listing services and listing management software vs service.
Where ListingBott fits in Washington execution
What ListingBott does
ListingBott is a workflow-based tool for directory submission that helps teams execute with structure, approvals, and clear status visibility.
How ListingBott works
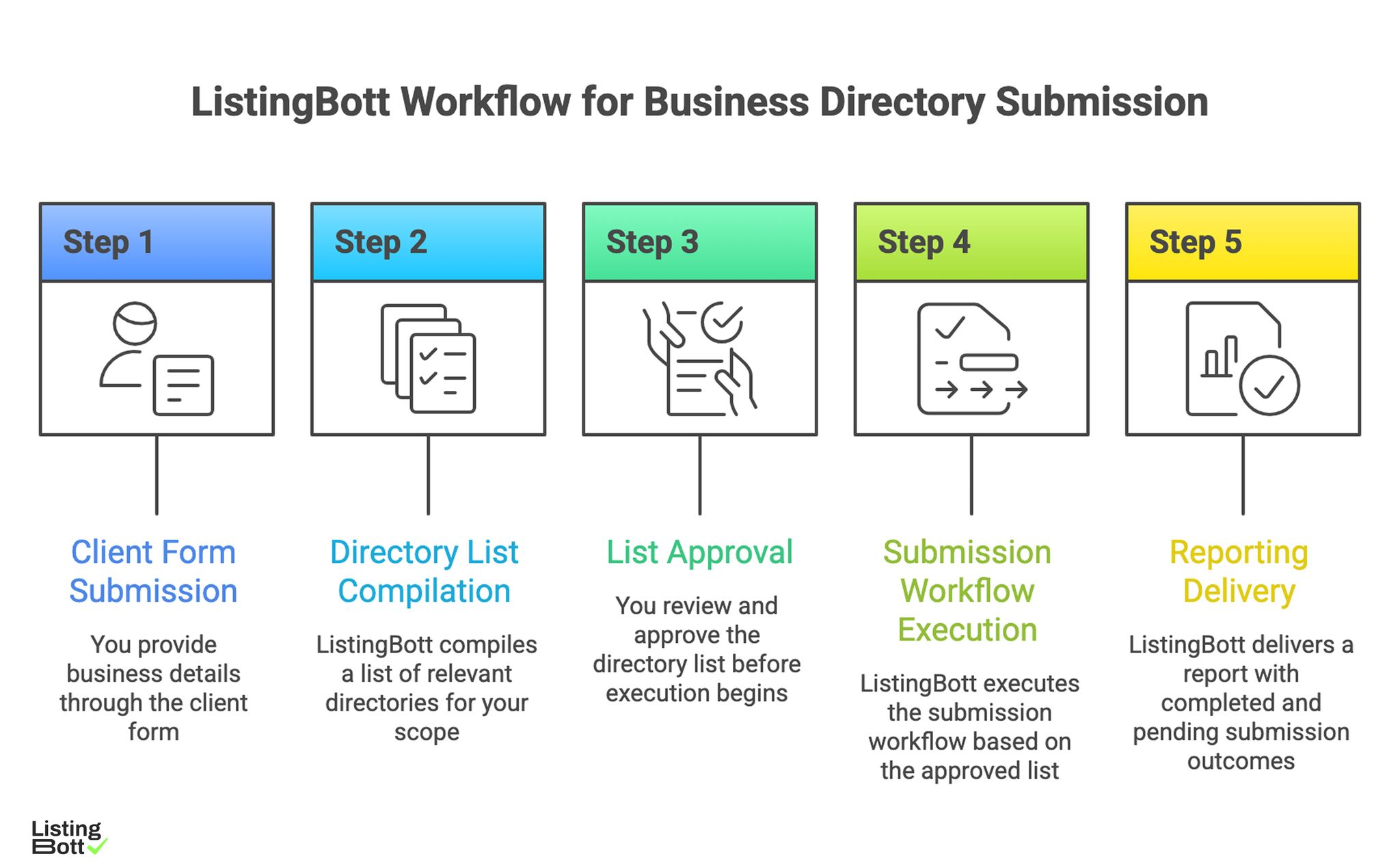
ListingBott Workflow for Business Directory Submission
-
You submit business details through the
client form. -
ListingBott compiles a
list of directoriesfor your scope. - You approve that list before execution starts.
- ListingBott executes submission workflow based on the approved list.
- ListingBott delivers reporting with completed and pending outcomes.
Key features and practical value
- Intake validation: lowers preventable profile-data errors before launch.
- Approval checkpoint: aligns scope and expectations early.
- Workflow transparency: supports owner coordination and escalation.
- Report handoff: enables quality review before next route expansion.
Teams usually get better outcomes by prioritizing workflow reliability over output-only claims.
Expected outcomes and limits
Expected outcomes:
- structured execution,
- clearer route-level visibility,
- repeatable process for additional rollout waves.
Limits to keep explicit:
- no guaranteed ranking position,
- no guaranteed traffic by a specific date,
- no guaranteed indexing speed,
- no guaranteed outcomes controlled by third-party platforms.
DR commitment is conditional only. A promise to reach DR 15 can apply when starting DR is below 15, the client explicitly selects domain growth, and the directory list is approved before execution starts. Refunds may apply if process has not started, with no hidden extra fees in current public offer language.
Risks/limits
Route-level failure patterns to avoid
- Launching routes without readiness score gates.
- Allowing route owners to override canonical data policy.
- Expanding when class 3 incidents are unresolved.
- Measuring throughput while ignoring correction quality.
- Running without explicit gate-owner accountability.
Practical limits
- Directory submission helps discoverability and consistency, but does not replace broader SEO systems.
- Impact timing varies by market, competition, and external platform behavior.
- Poor governance during expansion creates compounding quality debt.
Minimum control layer
- threshold-based route expansion,
- SLA-bound correction ownership,
- weekly route-level KPI review,
- mandatory approval artifacts per wave.
FAQ
Why use a route model for Washington?
Because operating conditions differ by route, and route-based control reduces one-size-fits-all errors.
Should all routes be launched in parallel?
Usually no. Launch priority routes first, stabilize, then expand.
Which metric is most important before route expansion?
Use route integrity pass rate together with critical issue age.
Can directory submission guarantee rankings?
No. It supports execution quality and discoverability, but rankings depend on external factors.
Is DR growth guaranteed by default?
No. DR commitments are conditional and apply only to qualified setups.
What is the minimum governance required?
Canonical data control, route gate ownership, correction SLA, and recurring route-level reporting.

