Quick answer
Local business directory submission in France works best with a structured rollout, not a submission sprint. The biggest risk is letting standards drift between waves, which causes slower approvals, slower fixes, and avoidable rework.
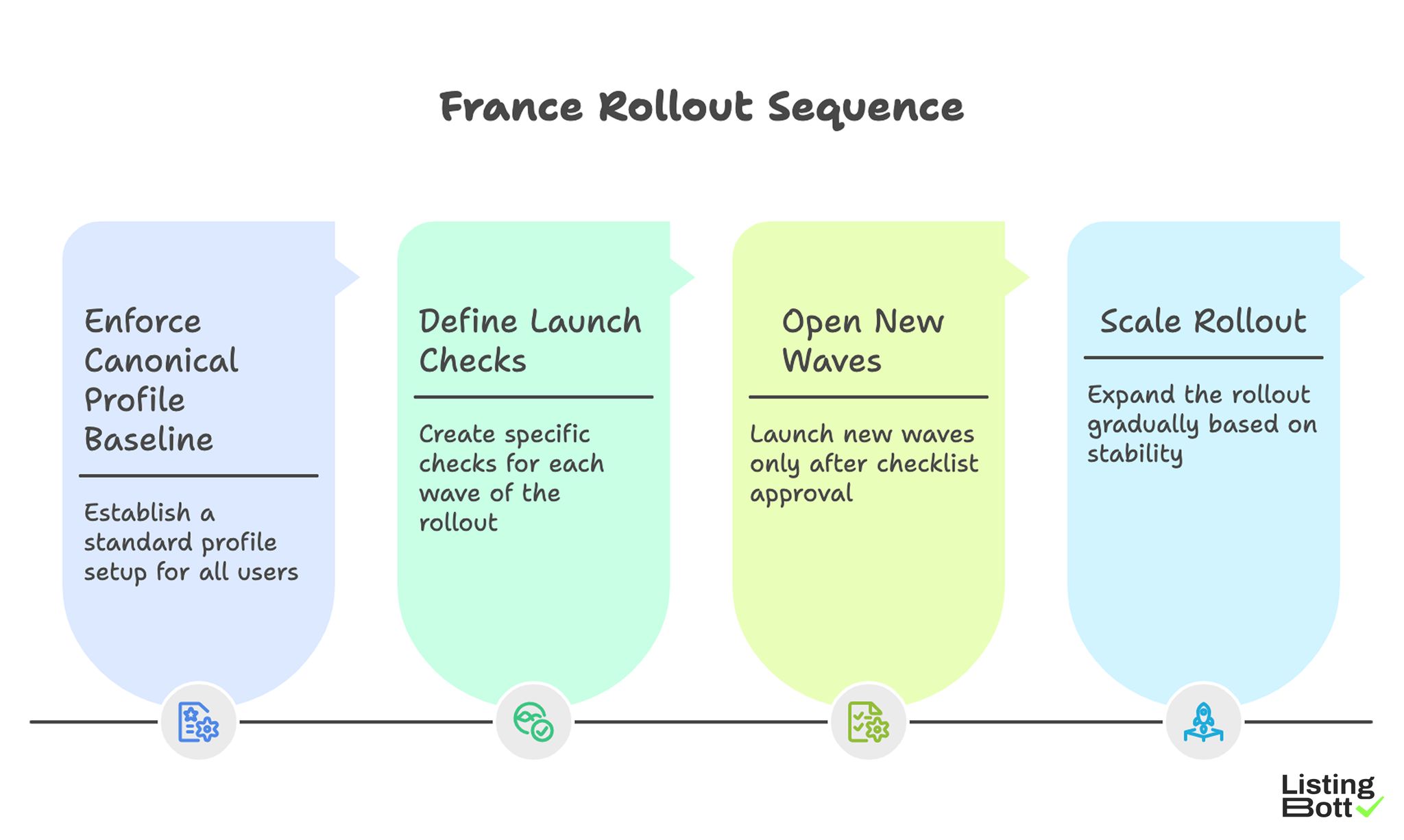
A practical France rollout sequence is:
- enforce one canonical profile baseline,
- define clear launch checks for each wave,
- open new waves only after checklist approval,
- scale only when quality and queue indicators remain stable.
For broader U.S. planning, see Local business directory submission USA.
France Rollout Sequence
sbb-itb-8e44301
Methodology
This page uses a France-specific rollout model focused on timing, correction speed, and clear expansion controls.
France rollout priorities
| Dimension | Weight | Operational role |
|---|---|---|
| Traceability | 15 | ensures every gate decision is documented and auditable |
| Rules stability | 15 | keeps profile and scope policy consistent across active waves |
| Intake quality | 15 | filters low-readiness records before execution starts |
| Cadence reliability | 10 | keeps review and decision timing predictable |
| Oversight clarity | 15 | assigns accountable owners for gate and escalation actions |
| Load control | 15 | aligns execution pace with correction capacity |
| Outcomes monitoring | 10 | validates that expansion quality remains stable |
| Recovery readiness | 5 | ensures rollback can happen without operational chaos |
Operating cadence:
- score each dimension from 1-5 every two weeks,
-
expansion blocks if
Rules stabilityorLoad controlis below 3, - expansion resumes only after two stable cycles with no blocker carryover.
Country rollout priorities
| Control domain | Objective | Primary KPI | Early failure sign |
|---|---|---|---|
| Policy control | keep one canonical baseline | baseline compliance rate | conflicting field rules in active wave |
| Scope control | prevent unapproved expansion | gate packet completeness | scope edits after approval |
| Correction control | maintain queue health and closure speed | high-severity closure velocity | rising age in blocker queue |
| Reporting control | ensure decisions use fresh evidence | dashboard freshness | stale KPI cards in decision meetings |
| Expansion control | approve only threshold-ready waves | launch readiness score | calendar-driven launches without score proof |
Rollout cycle map
| Cycle step | Key question | Required evidence | Block condition |
|---|---|---|---|
| Step 1: readiness intake | Is profile data complete and policy-conformant? | readiness checklist + validation log | missing mandatory fields |
| Step 2: scope authorization | Is wave scope approved and frozen? | signed inclusion/exclusion packet | unapproved scope delta |
| Step 3: controlled launch | Are owners and SLAs active before publish? | owner matrix + SLA card | missing gate owner |
| Step 4: post-launch audit | Are early quality signals in range? | integrity audit + queue snapshot | blocker queue threshold breach |
| Step 5: expansion vote | Can next wave open without raising risk? | readiness score + council notes | unstable trend over two cycles |
Approval checklist
| Packet section | Mandatory fields | Why it matters |
|---|---|---|
| Baseline section | canonical data policy + accepted variants | prevents conflicting profile rules |
| Scope section | approved included and excluded segments | eliminates hidden scope creep |
| Ownership section | gate owner, escalation owner, backup owner | avoids decision latency and handoff gaps |
| SLA section | closure targets by issue class | aligns correction speed with expansion pace |
| Reporting section | KPI panel links + freshness timestamps | keeps decision inputs current |
| Exception section | open exceptions and mitigation path | prevents unresolved risk from carrying forward |
Common issue types
| Class | Description | Impact level | Default ruling |
|---|---|---|---|
| C1 | local formatting inconsistency | low | batch correction in normal cycle |
| C2 | repeated policy mismatch in active wave | medium | conditional hold + focused correction sprint |
| C3 | cross-wave policy contradiction | high | expansion freeze and policy reset |
| C4 | gate decision without full evidence | high | immediate rollback to last approved scope |
A clear issue map improves decision speed and keeps escalation proportional to risk.
Queue priorities
| Lane | Entry trigger | Priority policy | Exit criteria |
|---|---|---|---|
| Lane L1 | low-impact consistency defects | process in weekly batch cycle | close inside normal review window |
| Lane L2 | repeated mismatch in active wave | prioritize over new launch tasks | close within weekly SLA |
| Lane L3 | systemic policy conflict or blocker issue | freeze expansion until resolved | clear before next expansion vote |
Review calendar
| Council | Frequency | Inputs | Output decision |
|---|---|---|---|
| Intake council | weekly | readiness pass/fail and rejection reasons | tighten or keep intake rules |
| Quality council | weekly | integrity trend, queue age, reopen ratio | continue, hold, or rollback |
| Expansion council | biweekly | TRICOLOR score + packet evidence | approve next wave or hold |
| Portfolio council | monthly | quality-cost trend + BOFU progression | rebalance roadmap and capacity |
Cost/effort trade-offs
| Control activity | Effort cost | Cost of skipping | Governance conclusion |
|---|---|---|---|
| Packet completeness review | moderate pre-launch effort | high post-launch rework cost | mandatory before every gate vote |
| Queue-lane audit | recurring weekly effort | hidden debt and delayed recovery | mandatory during active waves |
| Decision logging | low admin overhead | weak root-cause visibility | required for all approvals |
| Exception review | moderate monthly analysis | repeated unresolved failure patterns | required in portfolio council |
| Rollback rehearsal | planned operational time | failure under live incident pressure | required each quarter |
92-day execution roadmap
| Phase | Days | Focus | Exit criteria |
|---|---|---|---|
| Setup phase | 1-18 | baseline lock, packet standard, owner map, councils | setup package approved |
| Wave 1 baseline | 19-40 | launch first wave with strict QA and queue controls | stable integrity and closure trend |
| Stabilization window | 41-64 | reduce L2/L3 carryover and reopen drift | queue risk normalized |
| Controlled expansion | 65-92 | open additional waves through expansion council | no post-wave KPI regression |
Pre-wave compliance checklist
| Checklist item | Validation method | Pass threshold |
|---|---|---|
| Baseline adherence | random active-record audit | no conflicting baseline edits |
| Ownership completeness | owner matrix preflight | all gate and escalation owners assigned |
| SLA readiness | high-severity closure trend audit | two stable weekly cycles |
| Dashboard currency | KPI freshness verification | no stale decision panels |
| Evidence completeness | packet checklist validation | all required docs attached |
KPI reference
| KPI | Formula | Decision purpose |
|---|---|---|
| Intake acceptance rate | accepted records / evaluated records | validates intake quality and policy fit |
| Wave integrity rate | records passing audit / sampled records | validates consistency in live execution |
| High-severity closure velocity | high-severity issues closed per week | tracks correction throughput |
| Reopen ratio | reopened items / closed items | measures correction durability |
| Queue pressure index | weighted age of L2 and L3 queues | detects compounding debt risk |
| Decision latency | average hours from detection to action | monitors governance responsiveness |
Common scenarios
| Scenario | Leading indicator | Operational risk | Immediate response | Exit condition |
|---|---|---|---|---|
| Intake saturation | evaluated records increase sharply while acceptance drops | weak intake filters allow low-quality records into execution | tighten Stage 1 validation and reduce intake batch size | acceptance rate returns to control band |
| Queue inversion | L3 blockers grow faster than L2 closures | systemic issues consume correction capacity | freeze new launches and run blocker-specific correction sprint | L3 backlog returns below threshold |
| Owner transition gap | gate approver change during active wave | delayed approvals and unresolved escalations | activate backup approver and require handoff packet | approval latency returns within budget |
| Reporting blind spot | KPI dashboard freshness degrades in active wave | expansion decision quality declines | lock expansion vote until dashboards refresh | all mandatory KPI cards are current |
| Scope creep pulse | new requests appear after scope sign-off | uncontrolled expansion with poor traceability | reject unsanctioned scope changes and reopen scope gate | updated scope is reapproved with full evidence |
This scenario map makes responses explicit before pressure increases.
Backlog risk model
| Variable | Definition | Practical interpretation |
|---|---|---|
D |
open quality debt items in L2/L3 | unresolved correction workload |
A |
average age of debt items (days) | risk of delayed recovery |
R |
weekly closure rate for high-severity items | correction throughput |
I |
debt-interest score (D * A / max(R,1)) |
how quickly unresolved risk compounds |
Use the debt-interest score as an expansion guard:
-
If
Irises for two consecutive cycles, expansion must pause. -
If
Iremains flat while volume grows, keep current wave only. -
If
Ideclines for two cycles, expansion can proceed to next gate.
This model prevents teams from treating backlog growth as a temporary cosmetic issue.
Decision log template
| Ledger field | Example value type | Why required |
|---|---|---|
| Decision ID | unique gate identifier | links outcomes to exact approval event |
| Wave ID | active rollout class and cycle | ensures traceability across phases |
| Evidence refs | list of packet docs and dashboard snapshots | proves decision basis |
| Risk score | TRICOLOR weighted value at decision time | validates threshold-based governance |
| Assigned owners | gate owner + escalation owner + backup owner | prevents ownership ambiguity |
| Follow-up date | scheduled review checkpoint | enforces decision accountability |
A structured ledger supports reliable retrospectives and faster root-cause analysis.
Rollback readiness drills
| Drill | Trigger simulation | Pass condition | Remediation if failed |
|---|---|---|---|
| Scope rollback drill | unauthorized scope delta appears in active cycle | scope reverts within one governance cycle | freeze new approvals until rollback process passes |
| Queue drain drill | L3 blockers exceed threshold suddenly | blocker queue normalized before next vote | allocate dedicated correction capacity and suspend expansion |
| Dashboard recovery drill | missing KPI card during expansion vote | dashboard restored within 24 hours | decision deferment plus reporting escalation |
| Owner continuity drill | escalation owner unavailable during incident | backup owner assumes control without SLA breach | revise ownership matrix before next cycle |
Quarterly drill execution reduces operational shock during live exceptions.
Decision hygiene rules
| Rule | Requirement | Violation outcome |
|---|---|---|
| Evidence-first rule | no gate vote without complete packet references | automatic vote deferment |
| Freshness rule | KPI data used in vote must be current | expansion hold until refresh |
| Accountability rule | every vote must include named owners | gate invalidation |
| Reversibility rule | rollback path must be documented in advance | launch blocked |
| Exception closure rule | no open high-severity blocker at expansion vote | expansion denied |
Decision hygiene ensures expansion quality is not dependent on individual judgment style.
Comparison table
| Execution model | Best for | Strength | Tradeoff | France hub fit |
|---|---|---|---|---|
| Flat nationwide rollout | short pilot tests | quick startup | weak control over compliance drift | Low |
| Manual segmented rollout | narrow-scope teams | local flexibility | high coordination overhead and low repeatability | Medium-low |
| Managed compliance-cycle execution | teams needing controlled growth speed | structured process with lower internal load | depends on workflow transparency | Strong |
| Hybrid governance execution | teams with internal QA ownership | strongest control-throughput balance | requires strict owner accountability | Very strong |
Model selection by maturity
| Team maturity signal | Recommended model | Why |
|---|---|---|
| Limited internal ops capacity | Managed compliance-cycle execution | preserves controls with lower internal burden |
| Moderate maturity with growth targets | Hybrid governance | supports scale without losing oversight |
| High maturity and strong SOP | Hybrid or software-led | enables deeper control optimization |
| Recurring blocker instability | Managed pilot + governance reset | restores stable baseline before scale |
Weekly KPI board
| KPI | Why it matters | Expansion stop trigger |
|---|---|---|
| Intake acceptance rate | intake quality signal | sustained decline in active wave |
| Wave integrity rate | policy consistency signal | repeated wave-level drop |
| High-severity closure velocity | correction responsiveness | critical queue aging beyond SLA |
| Reopen ratio | correction durability signal | two-cycle upward trend |
| BOFU progression actions | commercial linkage signal | informational activity with weak progression |
Best by use case
1) Single-location launch
Best fit: managed compliance-cycle execution with clear packet governance.
Reason: keeps execution simple while preserving quality controls.
2) Multi-location rollout
Best fit: hybrid governance with evidence-based wave approvals.
Reason: scaling stays controlled and owner accountability remains explicit.
3) Product-led SaaS expansion
Best fit: phased rollout tied to policy and queue thresholds.
Reason: threshold-based expansion reduces correction debt risk.
4) Agency portfolio delivery
Best fit: standardized packet checks and lane-based escalation.
Reason: repeatable controls reduce cross-account variance.
5) Governance-sensitive environments
Best fit: approval-first workflow with full decision traceability.
Reason: documented controls improve reliability and audit readiness.
For benchmark references, compare workflow rigor and control depth through best directory listing services and best local business directories.
Where ListingBott fits in France execution
What ListingBott does
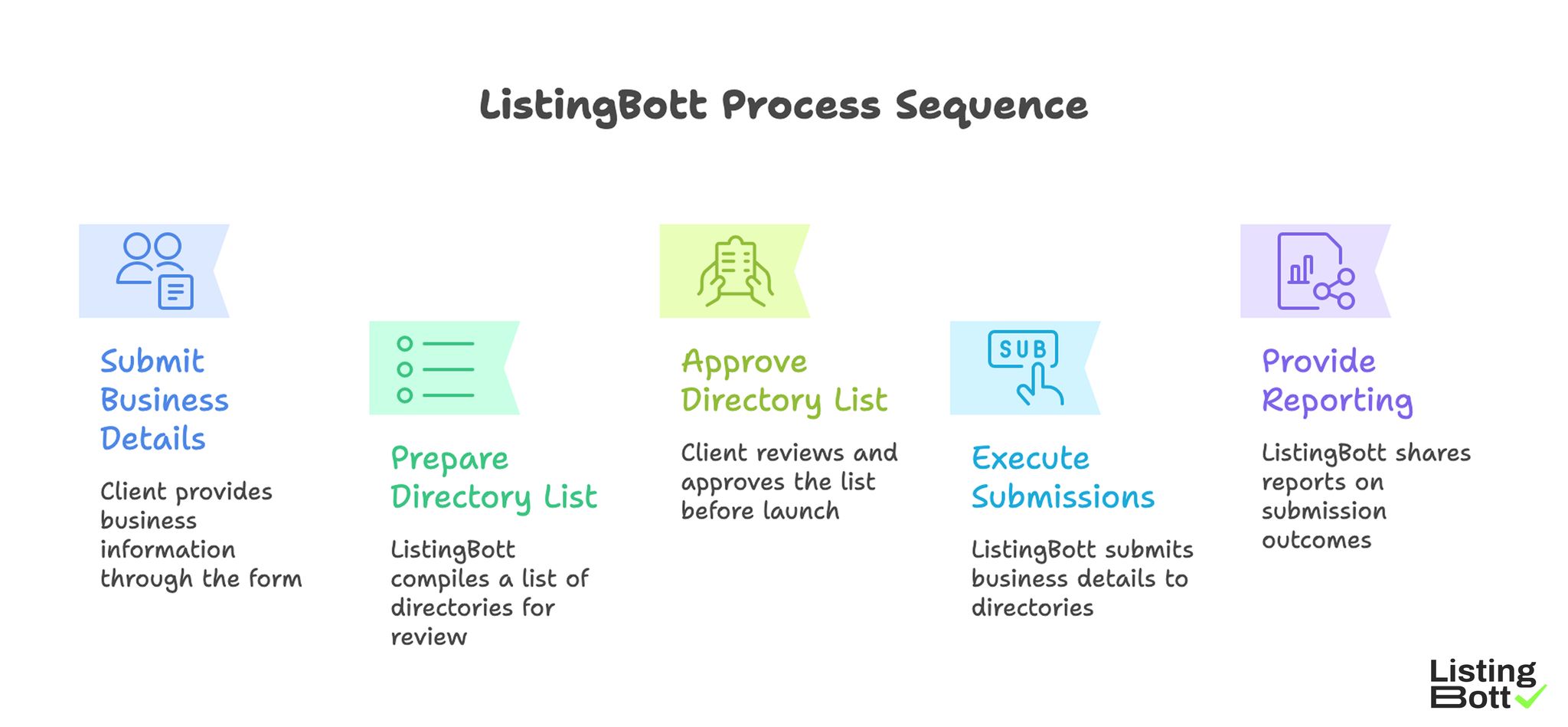
ListingBott is a workflow-based directory submission tool for teams that need structured execution, approval checkpoints, and transparent reporting.
How ListingBott works
-
You submit business details through the
client form. -
ListingBott prepares a
list of directoriesfor scope review. - You approve the list before launch starts.
- ListingBott executes submissions based on approved scope.
-
ListingBott provides reporting for completed and pending outcomes.
ListingBott Process Sequence
Key features and practical value
- Intake validation: reduces preventable profile-data errors before launch.
- Approval checkpoint: aligns scope and expectations before execution.
- Workflow transparency: supports ownership and escalation control.
- Reporting handoff: supports data-backed decisions before each wave.
Teams that prioritize workflow reliability usually maintain stronger long-term execution quality than teams focused only on submission volume.
Expected outcomes and limits
Expected outcomes:
- structured submission execution,
- clear wave-level visibility,
- repeatable process for additional expansion waves.
Limits to keep explicit:
- no guaranteed ranking position,
- no guaranteed traffic by a specific date,
- no guaranteed indexing speed,
- no guaranteed outcomes controlled by third-party platforms.
DR commitment is conditional only. A promise to reach DR 15 can apply when starting DR is below 15, the client explicitly selects domain growth, and the directory list is approved before process launch. Refunds may apply if process has not started, and public offer language remains no hidden extra fees.
Risks/limits
Common failure patterns
- Launching waves without complete evidence packets.
- Expanding while L3 queue issues remain unresolved.
- Running mixed baseline policy rules in active waves.
- Tracking output totals while ignoring queue and reopen trends.
- Escalating issues without clear owner accountability.
Practical limits
- Directory submission supports discoverability and consistency, but does not replace broader SEO systems.
- Timing and outcomes vary by category, competition, and third-party platform behavior.
- Expansion without packet and queue discipline can create compounding correction debt.
Minimum control layer
- wave-based gate approvals,
- SLA-bound correction ownership,
- weekly KPI and queue-lane review,
- complete evidence packet before each expansion decision.
FAQ
Why use a compliance-cycle model in France?
Because stable execution depends on synchronized governance timing, policy consistency, and queue discipline.
Should all waves launch in parallel?
Usually no. Launch sequentially, stabilize quality, then expand.
Which KPI should block expansion first?
Use high-severity closure velocity together with intake acceptance and wave-integrity rates.
Can directory submission guarantee rankings?
No. It supports consistency and discoverability, but rankings depend on external factors.
Is DR growth guaranteed for every project?
No. DR commitments are conditional and apply only to qualified setups.
What is the minimum governance stack?
Canonical data control, gate ownership, correction SLA, and recurring wave-level KPI reviews.


