Quick answer
Local business directory submission in Georgia is most reliable when you run a network-governance model: centralized standards with zone-level execution controls. Teams that use a single statewide rollout rhythm usually create uneven quality, delayed corrections, and avoidable rework.
A practical Georgia sequence is:
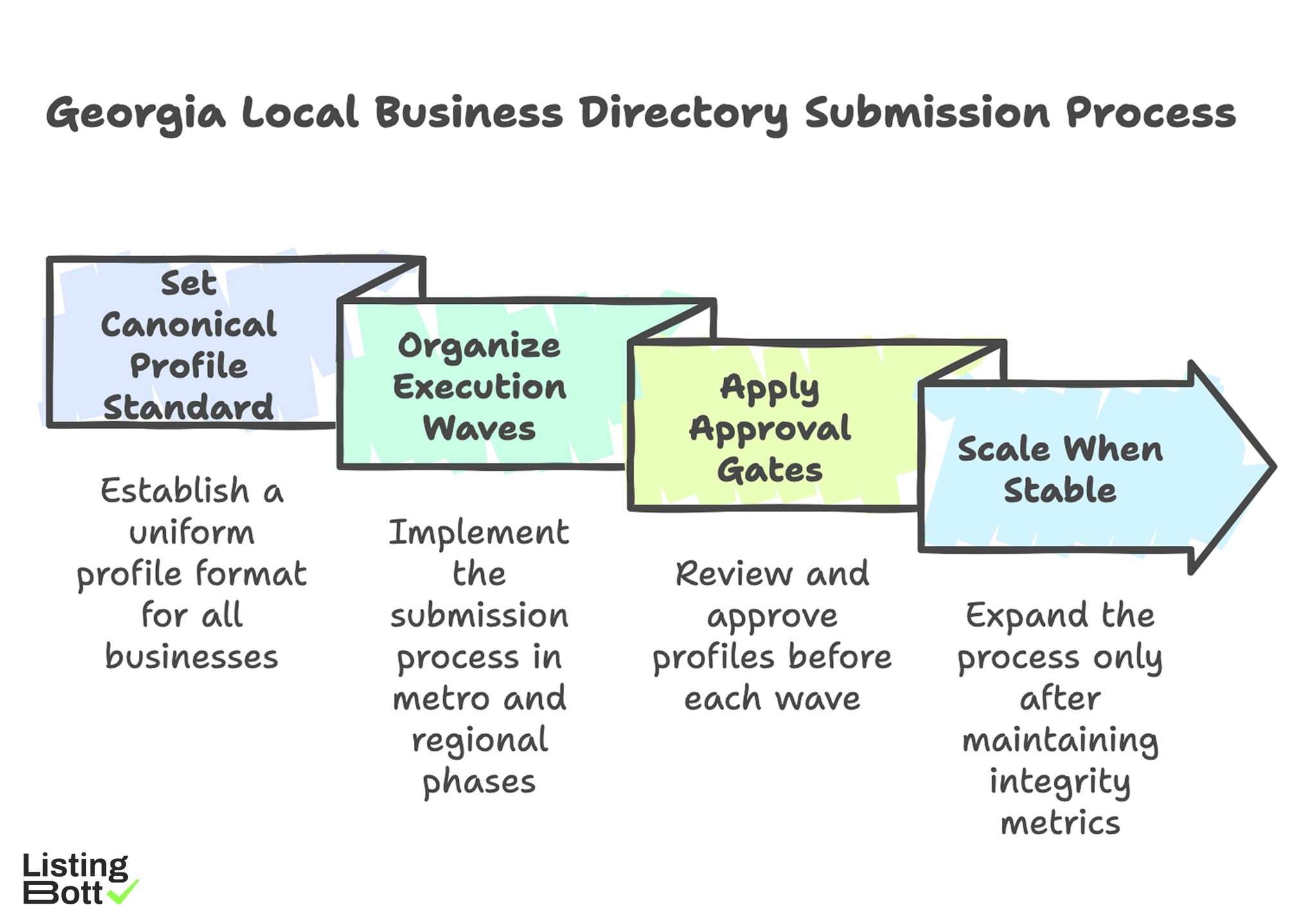
Georgia Local Business Directory Submission Process
- set one canonical profile standard,
- organize execution as metro-to-regional network waves,
- apply approval gates before each wave,
- scale only when integrity and correction metrics remain stable.
For broader U.S. planning, see Local business directory submission USA.
sbb-itb-8e44301
Methodology
This page uses a Georgia-specific governance method focused on distributed execution with centralized quality control.
The NODE framework (Normalization, Ownership, Decisioning, Escalation)
| Component | Weight | What it controls |
|---|---|---|
| Normalization | 30 | consistency of profile data across all active zones |
| Ownership | 25 | clear accountability for correction and approvals |
| Decisioning | 25 | objective go/no-go rules for expansion |
| Escalation | 20 | response quality for high-severity issues |
How to apply NODE:
- score each component from 1-5 biweekly,
-
pause expansion when
NormalizationorDecisioningis below 3, - resume only after two consecutive stable cycles.
NODE reduces reliance on ad hoc operational judgment during growth.
Georgia network zones
| Zone type | Example execution profile | Launch wave | Priority objective | Typical risk |
|---|---|---|---|---|
| Primary metro zone | high-activity local operations | 1 | establish strongest baseline controls | fast volume with weak correction coverage |
| Secondary metro zone | medium/high mixed activity | 1-2 | replicate baseline without drift | owner handoff inconsistencies |
| Regional growth zone | distributed moderate activity | 2 | expand with stable reporting cadence | delayed issue closure |
| Long-tail zone | broad low-activity coverage | 3 | add breadth under maintenance constraints | hidden backlog accumulation |
Governance board design
| Board | Cadence | Owner | Purpose |
|---|---|---|---|
| Quality board | weekly | QA lead | integrity trend, error categories, reopen patterns |
| Operations board | weekly | execution lead | SLA health, blocker aging, correction throughput |
| Expansion board | biweekly | program owner | readiness score and gate decisions |
| Strategy board | monthly | leadership | quality-cost profile and BOFU progression |
A board-based model keeps decisions traceable and reduces uncontrolled scope expansion.
Decision-gate logic
| Gate | When triggered | Required evidence | Expansion blocker |
|---|---|---|---|
| Gate 1: baseline approval | before first live submissions | canonical profile policy + owner map | conflicting profile sources |
| Gate 2: scope approval | before each network wave | approved inclusion/exclusion list | unapproved scope changes |
| Gate 3: quality verification | after initial wave batch | integrity report + issue taxonomy | high-severity issue threshold breach |
| Gate 4: capacity verification | before next wave | correction velocity trend + backlog pressure | unresolved critical issue age trend |
Issue taxonomy and actions
| Issue tier | Pattern | Impact | Required action |
|---|---|---|---|
| Tier 1 | formatting or minor metadata mismatch | low and localized | fix in normal correction cycle |
| Tier 2 | repeated profile inconsistency in active zone | medium and expandable | targeted correction sprint |
| Tier 3 | cross-zone data integrity breakdown | high and systemic | freeze expansion + root-cause response |
Tiered issue handling helps prevent local errors from becoming network-wide quality debt.
86-day Georgia rollout map
| Phase | Window | Focus | Exit criteria |
|---|---|---|---|
| Governance setup | Days 1-15 | policy lock, ownership map, gate definitions | governance package approved |
| Wave 1 launch | Days 16-36 | launch primary metro zone with strict QA controls | integrity and SLA trends stable |
| Stabilization cycle | Days 37-56 | reduce tier 2/3 issue age and reopen rate | issue trend normalized |
| Wave 2-3 expansion | Days 57-86 | extend to secondary and regional zones by readiness | no post-wave KPI regression |
Skipping stabilization usually causes growth with unresolved correction debt.
Pre-launch and expansion checklist
| Checkpoint | Validation | Pass condition |
|---|---|---|
| Canonical source lock | one profile source for all active zones | no conflicting edits |
| Ownership map | gate owner + escalation owner assigned | full owner map active |
| SLA compliance | high-severity closure targets on trend | stable weekly compliance |
| Reporting readiness | zone-level dashboards updated on schedule | complete weekly visibility |
| Gate artifact completeness | all required approvals attached per wave | no missing artifacts |
Comparison table
| Execution approach | Best for | Strength | Tradeoff | Georgia fit |
|---|---|---|---|---|
| One-speed statewide rollout | short pilot tests only | fast startup | weak quality resilience at scale | Low |
| Manual segmented operations | small teams with limited footprint | local flexibility | low repeatability and high coordination overhead | Medium-low |
| Managed network execution | teams needing speed with control | structured delivery with lower internal load | depends on transparent process handoff | Strong |
| Hybrid governance model | teams with internal QA ownership | best balance of control and expansion speed | requires strict role boundaries | Very strong |
Model selection by team profile
| Team signal | Recommended model | Rationale |
|---|---|---|
| Limited internal ops capacity | Managed network execution | keeps governance quality without heavy internal burden |
| Moderate maturity with growth pressure | Hybrid governance | supports scale while preserving internal oversight |
| High maturity and strong SOP | Hybrid or software-led | enables deeper internal control design |
| Repeated correction instability | Managed pilot + governance reset | restores baseline before additional expansion |
Weekly KPI board
| KPI | Why it matters | Expansion stop trigger |
|---|---|---|
| Integrity pass rate by zone | measures quality stability by wave | sustained decline in active zone |
| High-severity closure velocity | tracks correction responsiveness | critical issues aging beyond SLA |
| Reopen ratio | measures correction durability | persistent multi-week increase |
| Backlog pressure | reflects operational debt | rising trend over two cycles |
| BOFU progression actions | ties execution to business outcomes | informational activity with weak progression |
If KPI reviews focus only on output count, quality debt usually goes undetected.
Best by use case
1) Single-location operator
Best fit: managed network execution with clear status reporting.
Reason: controls remain visible while day-to-day operational burden stays low.
2) Multi-location team
Best fit: hybrid governance with zone-gated expansion.
Reason: growth remains measurable and owner accountability stays explicit.
3) Product-led SaaS team
Best fit: phased rollout governed by readiness thresholds.
Reason: threshold-driven expansion lowers risk of correction backlog growth.
4) Agency managing multiple clients
Best fit: standardized issue taxonomy and escalation protocol.
Reason: repeatable execution and fast intervention reduce variability.
5) Governance-heavy organization
Best fit: approval-first workflow with full decision artifacts.
Reason: traceability supports consistency and compliance reviews.
For benchmark context while evaluating solutions, compare governance depth and execution clarity on best directory listing services and listing management software vs service.
Where ListingBott fits in Georgia execution
What ListingBott does
ListingBott is a workflow-based tool for directory submission built for teams that need structured execution, explicit approvals, and transparent reporting.
How ListingBott works
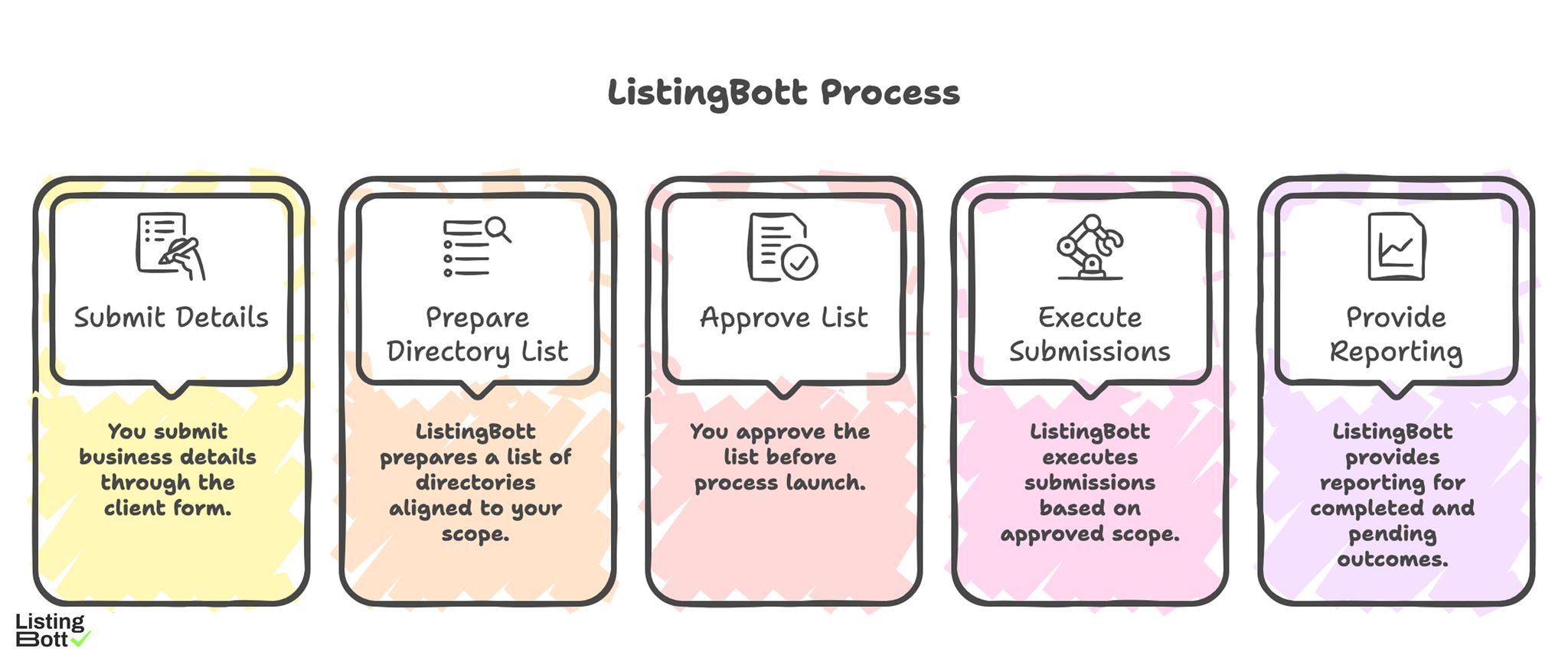
ListingBott Process
-
You submit business details through the
client form. -
ListingBott prepares a
list of directoriesaligned to your scope. - You approve the list before process launch.
- ListingBott executes submissions based on approved scope.
- ListingBott provides reporting for completed and pending outcomes.
Key features and practical value
- Intake validation: reduces preventable data-quality issues before launch.
- Pre-publish approval: aligns scope and expectations early.
- Workflow transparency: supports owner coordination and escalation.
- Reporting handoff: enables quality decisions before each next wave.
Teams that prioritize workflow reliability generally preserve better long-term execution quality than teams optimized only for volume.
Expected outcomes and limits
Expected outcomes:
- structured submission execution,
- clear operational visibility,
- repeatable process for expansion waves.
Limits to keep explicit:
- no guaranteed ranking position,
- no guaranteed traffic by a specific date,
- no guaranteed indexing speed,
- no guaranteed outcomes controlled by third-party platforms.
DR commitment is conditional only. A promise to reach DR 15 can apply when starting DR is below 15, the client explicitly selects domain growth, and the directory list is approved before process launch. Refunds may apply if process has not started, and public offer language remains no hidden extra fees.
Risks/limits
Frequent Georgia rollout mistakes
- Launching additional zones before governance artifacts are complete.
- Treating all zones as operationally identical.
- Expanding while tier 3 issues are unresolved.
- Tracking submission volume without reopen and backlog trend checks.
- Running escalation without named owner accountability.
Practical limits
- Directory submission supports discoverability and consistency, but does not replace broader SEO systems.
- Timing and impact vary by category, competition, and third-party platform behavior.
- Uncontrolled expansion can create compounding correction debt.
Minimum control layer
- wave-based gate approvals,
- SLA-bound correction ownership,
- weekly KPI review by zone,
- required artifacts before every expansion wave.
FAQ
Why use a governance model in Georgia?
Because quality stability depends on consistent standards, clear ownership, and controlled expansion decisions.
Should all zones launch in parallel?
Usually no. Launch by waves, stabilize metrics, then expand.
Which KPI should stop expansion first?
Use high-severity closure velocity with zone integrity pass rate.
Can directory submission guarantee rankings?
No. It supports consistency and discoverability, but rankings depend on external factors.
Is DR growth guaranteed for every project?
No. DR commitments are conditional and apply only to qualified setups.
What is the minimum governance stack?
Canonical data control, gate ownership, correction SLA, and recurring zone-level KPI review.


