Quick answer
Local business directory submission in Delaware should be run as a corridor-based program with one governance layer across all operating zones. The state is compact, but execution still breaks when teams treat all areas as identical and skip approval controls.
A practical Delaware sequence is:
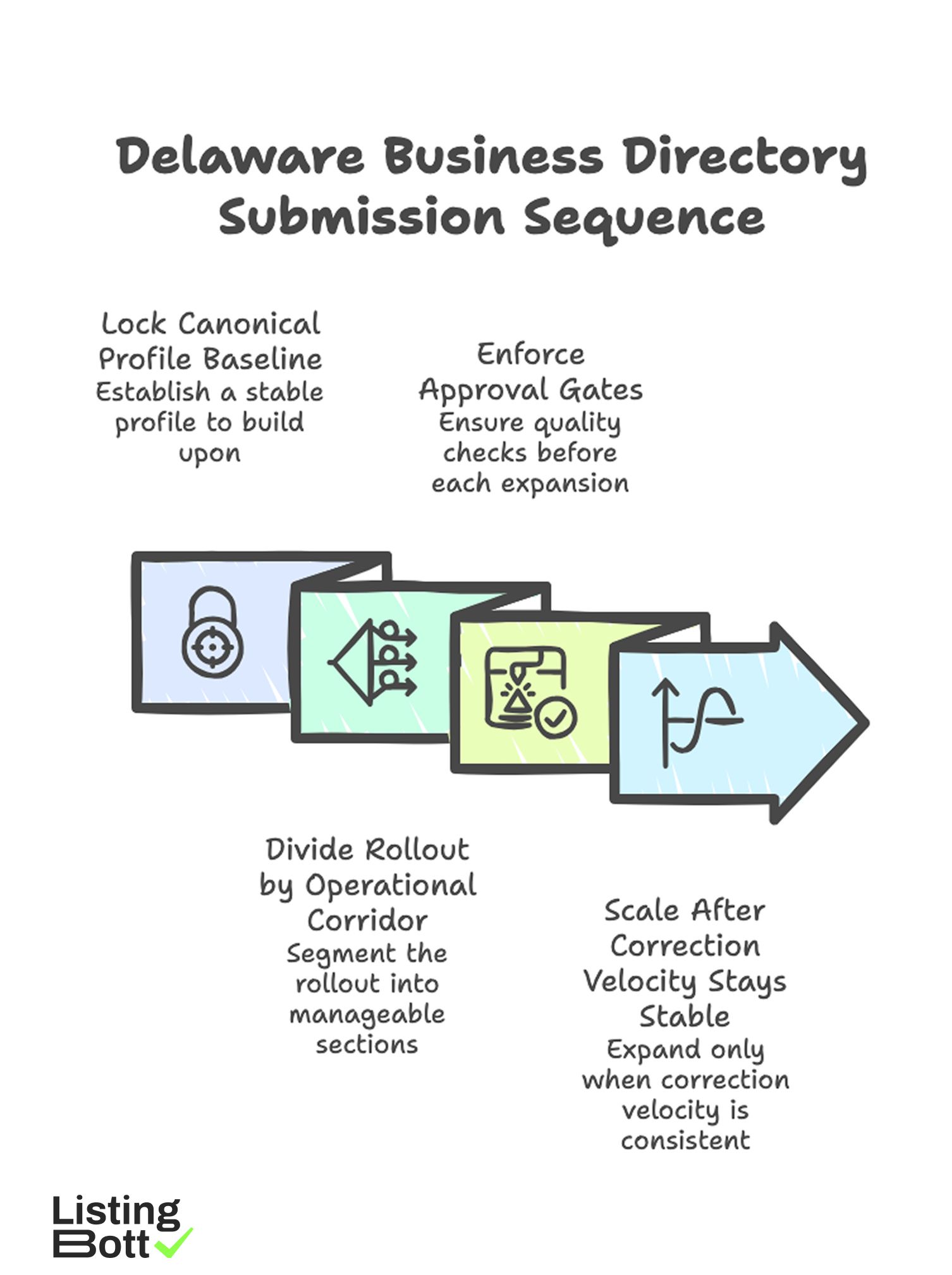
Delaware Business Directory Submission Sequence
- lock one canonical profile baseline,
- divide rollout by operational corridor,
- enforce approval gates before each expansion step,
- scale only after correction velocity stays stable.
For broader U.S. planning, see Local business directory submission USA.
sbb-itb-8e44301
Methodology
This page uses a Delaware-specific operating framework focused on compact-state coverage, cross-corridor consistency, and correction control.
The CORE model (Corridors, Ownership, Review, Expansion)
| Factor | Weight | Why it matters in Delaware |
|---|---|---|
| Corridor design | 25 | Prevents uneven execution when conditions vary by local area |
| Ownership clarity | 25 | Keeps issue resolution accountable across teams |
| Review cadence | 30 | Detects quality drift before it scales |
| Expansion discipline | 20 | Stops growth before QA throughput is ready |
How to run CORE:
- score each factor from 1-5 every two weeks,
-
freeze expansion if
OwnershiporReviewdrops below 3, - reopen growth only when critical correction backlog normalizes.
This keeps execution controlled when volume rises.
Delaware corridor map
| Corridor | Wave | Main objective | Typical risk | Expansion gate |
|---|---|---|---|---|
| North corridor | 1 | establish baseline quality and correction workflow | rapid scope growth without governance | critical issues closed within SLA |
| Central corridor | 1-2 | replicate baseline with low variance | mixed source data standards | integrity pass rate aligns with north corridor |
| South corridor | 2 | scale coverage with stable process | delayed ownership handoffs | named owner + escalation route active |
| Long-tail coverage | 3 | controlled breadth expansion | hidden backlog growth | backlog below threshold for two cycles |
Operational governance matrix
| Cadence | Role owner | What is reviewed | Decision output |
|---|---|---|---|
| Daily | Execution lead | new exceptions and blocking errors | immediate fix assignment |
| Weekly | QA owner | integrity trend, correction age, lane variance | continue, hold, or rollback region scope |
| Biweekly | Program owner | readiness score and expansion gates | approve or freeze next wave |
| Monthly | Stakeholders | quality-cost trend and BOFU progression | capacity + priority update |
When cadence is skipped, execution debt usually appears before teams see it in summary dashboards.
75-day Delaware rollout blueprint
| Phase | Days | Focus | Exit condition |
|---|---|---|---|
| Foundation | 1-14 | canonical data standard, owner mapping, gate policy | baseline approved |
| Initial execution | 15-32 | launch north corridor with QA controls | pass rate and correction speed stable |
| Replication | 33-52 | extend to central and south corridors | no quality regression after expansion |
| Controlled scale | 53-75 | add long-tail coverage with backlog controls | thresholds hold for two review cycles |
Compact geography does not remove operational complexity. It only changes how quickly mistakes propagate.
Pre-expansion checklist
| Checkpoint | Validation question | Pass criteria |
|---|---|---|
| Canonical source | Is one source-of-truth enforced for profile data? | Yes, no competing baselines |
| Scope approval | Is inclusion/exclusion approved before execution? | Yes, formal gate exists |
| Correction SLA | Are critical fix timelines defined and tracked? | Yes, weekly review active |
| Corridor reporting | Can performance be read by corridor and wave? | Yes, segmented reporting exists |
| Expansion block rule | Is growth blocked on measurable thresholds? | Yes, threshold logic documented |
Comparison table
| Execution model | Best for | Strengths | Tradeoffs | Delaware suitability |
|---|---|---|---|---|
| Manual spreadsheet process | very small pilot scope | simple setup | weak scalability and low auditability | Low |
| Internal software-led process | teams with mature QA operations | strong control and traceability | requires disciplined governance | Medium |
| Managed execution model | teams needing faster rollout with process controls | lower operator load and clearer throughput | needs transparent workflow partner | Strong |
| Hybrid governance model | teams balancing speed and strict QA | combines scalability with internal oversight | requires explicit role boundaries | Often strongest |
Model fit by team maturity
| Team state | Recommended model | Why |
|---|---|---|
| Limited internal bandwidth | Managed execution | protects control without heavy internal ops burden |
| Moderate bandwidth with growth pressure | Hybrid governance | enables scale with enforceable quality checks |
| Strong SOP and QA maturity | Software-led or hybrid | supports deeper internal control |
| Backlog instability | Managed pilot + governance reset | stabilizes operations before expansion |
Delaware KPI stack
| KPI | Why it matters | Warning signal |
|---|---|---|
| Integrity pass rate by corridor | core quality indicator | sustained decline in any active corridor |
| Critical-fix closure velocity | measures response speed | aging high-priority issues |
| Expansion readiness score | prevents calendar-driven launches | score below defined threshold |
| Backlog pressure index | tracks operational debt | upward trend across review cycles |
| BOFU progression actions | links execution to commercial outcomes | informational traffic with weak actions |
Teams that evaluate only submission count usually discover quality problems too late.
Best by use case
1) Single-location business
Best fit: managed execution with strict correction visibility.
Reason: it keeps operations straightforward while preserving quality controls.
2) Multi-location operator across Delaware
Best fit: hybrid governance with corridor-level checkpoints.
Reason: this supports controlled scale without losing accountability.
3) SaaS team building local discoverability
Best fit: phased rollout tied to readiness thresholds.
Reason: launch quality remains stable when expansion follows data, not deadlines.
4) Agency programs with multiple clients
Best fit: standardized workflow with explicit owner mapping.
Reason: agencies need repeatable delivery and fast escalation paths.
5) Compliance-sensitive organizations
Best fit: approval-first model with audit-ready process records.
Reason: formal gating reduces variance and improves traceability.
For vendor evaluation context, compare execution models with practical operating criteria using best directory listing services and best local business directories.
Where ListingBott fits in Delaware execution
What ListingBott does
ListingBott is a tool-based directory submission workflow for teams that need structured execution, clear ownership, and visible status tracking.
How ListingBott works
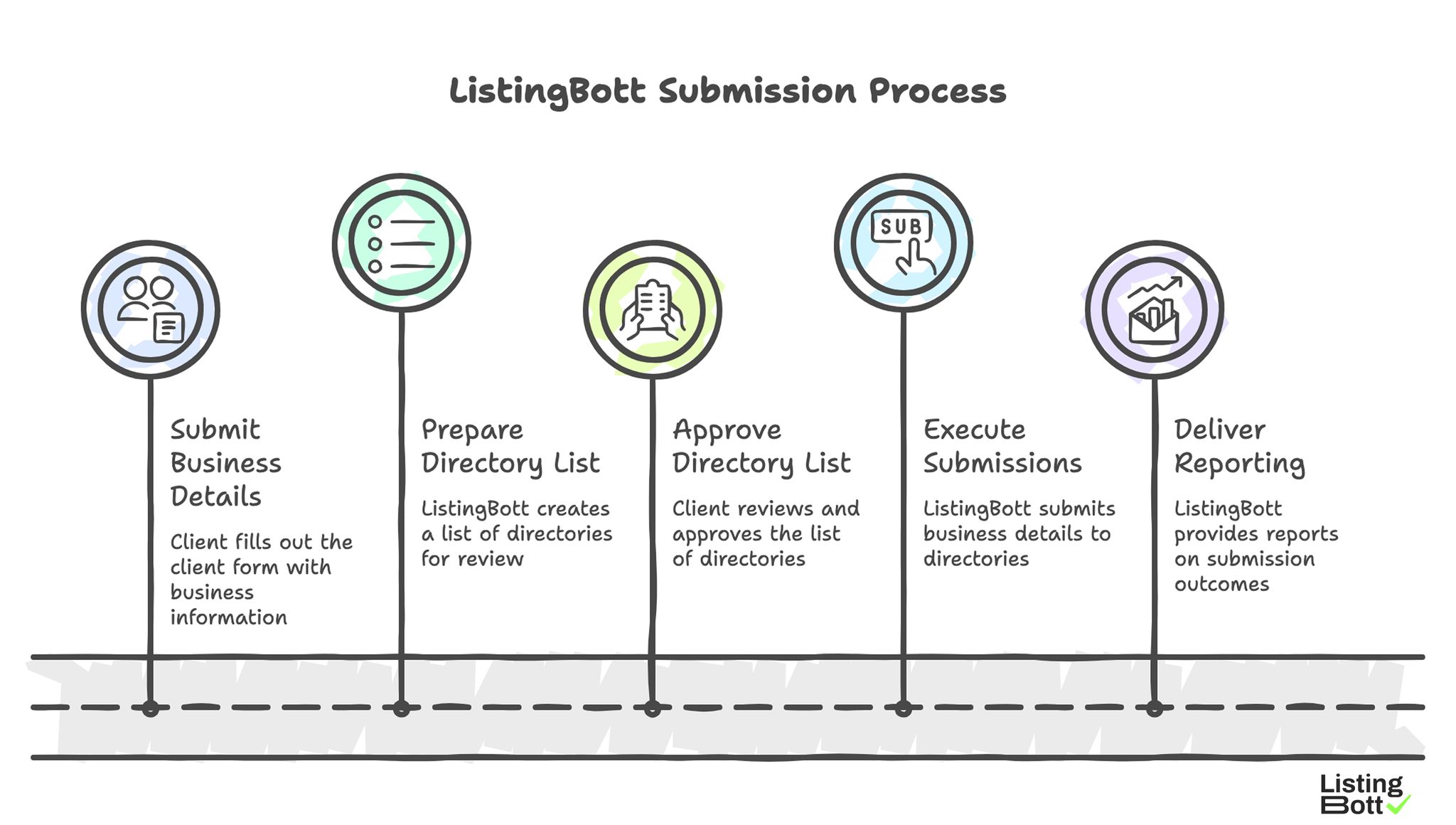
ListingBott Submission Process
-
You submit business details via the
client form. -
ListingBott prepares a
list of directoriesfor review. - You approve the list before process launch.
- ListingBott executes submissions based on approved scope.
- ListingBott delivers reporting for completed and pending outcomes.
Key features and operational meaning
- Intake validation: catches profile-data issues before launch.
- Approval-before-publish: aligns scope and expectations early.
- Workflow transparency: supports team coordination and escalation.
- Reporting handoff: enables quality checks before next-wave expansion.
Teams typically get better long-term outcomes by choosing workflow reliability over scale claims that ignore quality controls.
Expected outcomes and limits
Expected outcomes:
- structured submission execution,
- better status visibility,
- repeatable process for additional rollout waves.
Limits to keep explicit:
- no guaranteed ranking position,
- no guaranteed traffic by a specific date,
- no guaranteed indexing speed,
- no guarantees for outcomes controlled by third-party platforms.
DR commitment is conditional only. A promise to reach DR 15 can apply when starting DR is below 15, the client explicitly selects domain growth, and the directory list is approved before execution. Refunds may apply if process has not started, with no hidden extra fees in current public offer language.
Risks/limits
Common rollout mistakes
- Treating all corridors as one uniform market with one launch speed.
- Expanding without corridor-level quality checks.
- Running execution while critical correction backlog grows.
- Measuring output volume only and ignoring fix velocity.
- Operating without explicit gate ownership and escalation rules.
Practical limits
- Directory submission supports discoverability and consistency, but does not replace broader SEO foundations.
- Outcome timing depends on category, competitive pressure, and third-party platform behavior.
- Fast expansion without governance can create quality debt that slows future growth.
Risk controls to enforce
- corridor-based rollout gates,
- SLA-bound correction ownership,
- recurring corridor status review,
- expansion freeze rules when thresholds fail.
FAQ
Why use corridor-based planning in Delaware?
Because local operating conditions still vary, and segmented rollout prevents one-size-fits-all errors.
Should all areas launch at once?
Usually no. Launch by corridor, stabilize quality, then expand.
Which metrics should stop expansion?
Use integrity pass rate, critical-fix closure velocity, and backlog pressure index.
Can directory submission guarantee rankings?
No. It supports quality and discoverability, but ranking outcomes depend on external factors.
Is DR growth automatically promised?
No. DR commitments are conditional and apply only to qualified setups.
What is the minimum governance layer for stable rollout?
Canonical profile control, named gate owners, correction SLA, and recurring status cadence.

