Quick answer
Local business directory submission in Arizona should be managed as a capacity planning problem, not only a submission output problem. Teams often scale early, then lose consistency because correction throughput and approval discipline were never sized for expansion.
A practical Arizona sequence is:
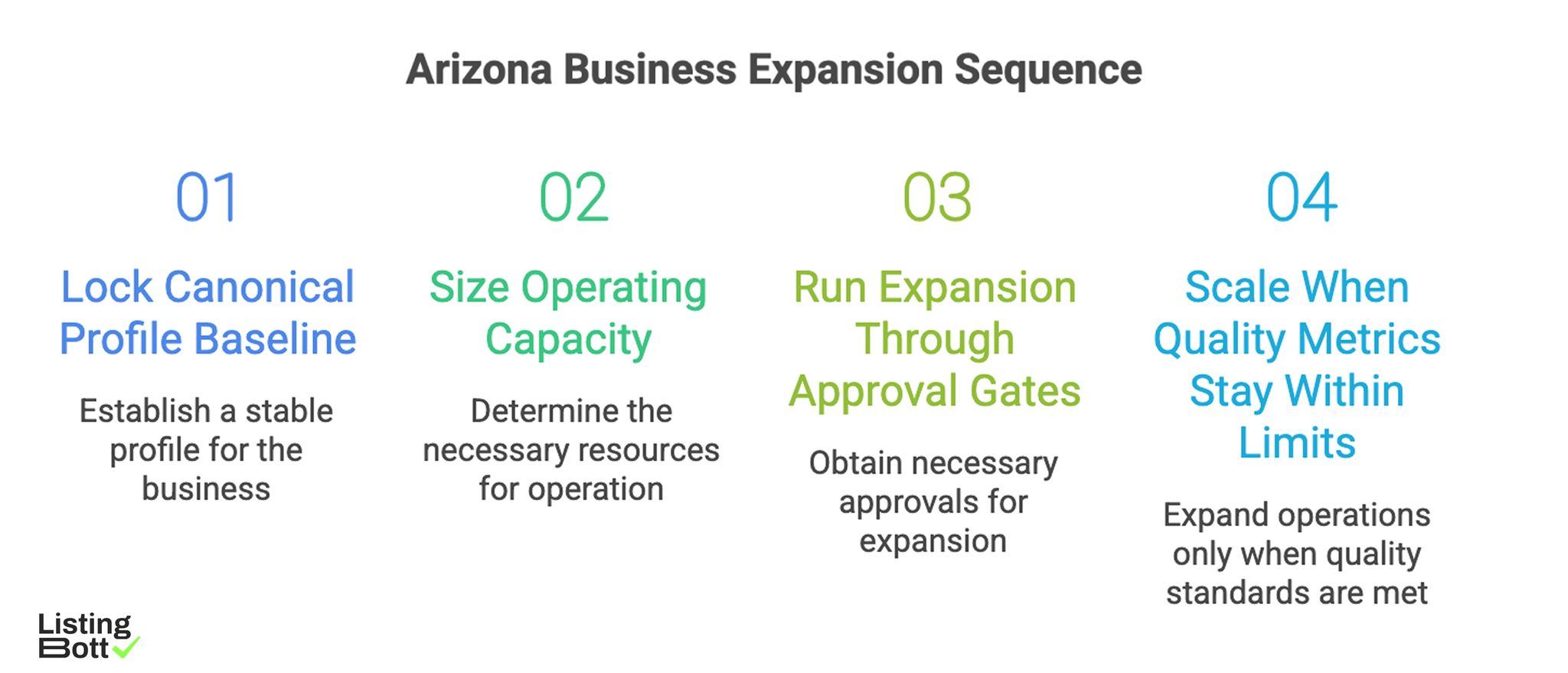
Arizona Business Expansion Sequence
- lock one canonical profile baseline,
- size operating capacity before launch,
- run expansion through approval gates,
- scale only when quality and correction metrics stay within limits.
For broader U.S. planning, see Local business directory submission USA.
sbb-itb-8e44301
Methodology
This page uses a capacity-first model for Arizona where execution pace is tied to measurable correction and governance capacity.
The SCALE-C model (Sizing, Controls, Accountability, Load, Evaluation, Cadence)
| Pillar | Weight | Why it matters |
|---|---|---|
| Sizing discipline | 20 | Prevents taking on more coverage than the team can maintain |
| Control quality | 25 | Maintains profile consistency during expansion |
| Accountability | 20 | Ensures correction ownership is explicit by wave |
| Load management | 20 | Keeps backlog from compounding during growth |
| Evaluation rigor | 10 | Detects drift before it becomes systemic |
| Cadence reliability | 5 | Preserves recurring decision rhythm under pressure |
How to apply SCALE-C:
- score each pillar 1-5 every two weeks,
-
block expansion when
Control qualityorLoad managementis below 3, - reopen expansion after two stable review cycles.
This turns expansion into a controlled decision instead of a calendar event.
Arizona capacity lanes
| Lane | Purpose | Primary KPI | Common failure mode | Launch gate |
|---|---|---|---|---|
| Core lane | establish baseline execution quality | integrity pass rate | rushing scope without QA maturity | baseline pass threshold met |
| Growth lane | extend coverage under controls | critical-fix closure velocity | backlog increase during expansion | SLA trend stable |
| Stabilization lane | reduce issue age and reopen rate | reopen rate | recurring issue loops | reopen trend improving |
| Scale lane | add additional coverage waves | readiness score | expansion with unresolved critical issues | all gates pass |
Capacity budget table
| Capacity component | Minimum planning rule | Warning sign |
|---|---|---|
| Review bandwidth | weekly QA window per active lane | skipped QA cycle |
| Correction bandwidth | named owner + SLA for critical issues | critical issue age rising |
| Approval bandwidth | gate owner available before launch | unapproved scope edits |
| Reporting bandwidth | lane-level dashboard update cadence | delayed or missing lane metrics |
A capacity budget prevents hidden overload when scope grows.
Approval-gate sequence
| Gate | Trigger point | Required evidence | Stop condition |
|---|---|---|---|
| Gate 1: baseline lock | before first submission | canonical profile policy + owner map | multiple active profile baselines |
| Gate 2: scope lock | before each expansion wave | approved inclusion/exclusion set | scope changed without sign-off |
| Gate 3: quality check | after initial wave batch | integrity report + issue classification | critical issues above threshold |
| Gate 4: capacity check | before next wave | SLA trend + backlog pressure score | unresolved capacity breach |
88-day Arizona rollout timeline
| Phase | Days | Focus | Exit criteria |
|---|---|---|---|
| Setup | 1-16 | profile baseline, owner assignment, gate policy | baseline approved |
| First execution wave | 17-36 | launch core lane with strict QA controls | pass rate and fix velocity stable |
| Stabilization sprint | 37-58 | reduce issue age and reopen rate | critical issue backlog controlled |
| Expansion wave | 59-88 | controlled scale via growth/scale lanes | no KPI regression post-expansion |
Skipping stabilization often leads to fragile growth and repeated correction work.
Pre-expansion checklist
| Checkpoint | Validation question | Pass criteria |
|---|---|---|
| Canonical source | Is one profile source enforced across active lanes? | Yes, no dual-source edits |
| Scope approval | Is expansion scope approved before launch? | Yes, gate evidence recorded |
| Correction SLA | Are critical issue targets tracked weekly? | Yes, trend visible |
| Lane reporting | Are metrics visible by lane and wave? | Yes, segmented reporting available |
| Expansion freeze rule | Is there a hard stop when thresholds fail? | Yes, documented and enforced |
Comparison table
| Execution model | Best for | Strengths | Tradeoffs | Arizona suitability |
|---|---|---|---|---|
| Flat statewide rollout | small short-term tests | easy to start | weak resilience under growth load | Low |
| Manual operations with ad hoc checks | very small teams | flexible adjustments | high coordination cost and inconsistent quality | Medium-low |
| Managed execution model | teams needing faster rollout with guardrails | lower internal overhead and clearer process | requires transparent provider workflow | Strong |
| Hybrid governance model | teams balancing speed and control | strong control-to-scale balance | depends on clear role boundaries | Very strong |
Model fit by operating maturity
| Team maturity pattern | Recommended model | Why |
|---|---|---|
| Limited internal capacity | Managed execution | preserves control without heavy internal load |
| Moderate capacity with growth targets | Hybrid governance | supports scale under explicit gates |
| Strong process maturity | Hybrid or software-led | enables deeper internal control |
| Persistent correction debt | Managed pilot + governance reset | stabilizes before broad expansion |
Weekly KPI stack
| KPI | Why it matters | Hold-expansion trigger |
|---|---|---|
| Integrity pass rate by lane | measures quality stability | sustained lane decline |
| Critical-fix closure velocity | tracks correction responsiveness | unresolved critical items past SLA |
| Reopen rate | tests correction quality | rising reopen trend |
| Backlog pressure score | measures operational debt | consecutive week-over-week increase |
| BOFU progression actions | links execution to business outcomes | informational visits with weak progression |
Counting submissions alone is not enough to protect long-term performance.
Best by use case
1) Single-location team
Best fit: managed execution with explicit quality reporting.
Reason: operations stay simple while controls remain visible.
2) Multi-location operator
Best fit: hybrid governance with lane-based expansion gates.
Reason: scaling decisions stay measurable and accountable.
3) Product-led SaaS team
Best fit: phased expansion based on readiness and capacity thresholds.
Reason: this reduces risk of overexpansion and correction debt.
4) Agency delivery workflow
Best fit: standardized process with issue-class escalation rules.
Reason: agencies need predictable execution across multiple accounts.
5) Governance-sensitive programs
Best fit: approval-first model with documented gate artifacts.
Reason: traceable decisions improve reliability and oversight.
For evaluation benchmarks, compare operating depth and conversion fit using best directory listing services and listing management software vs service.
Where ListingBott fits in Arizona execution
What ListingBott does
ListingBott is a workflow-based tool for directory submission that helps teams run structured execution with approvals and status visibility.
How ListingBott works
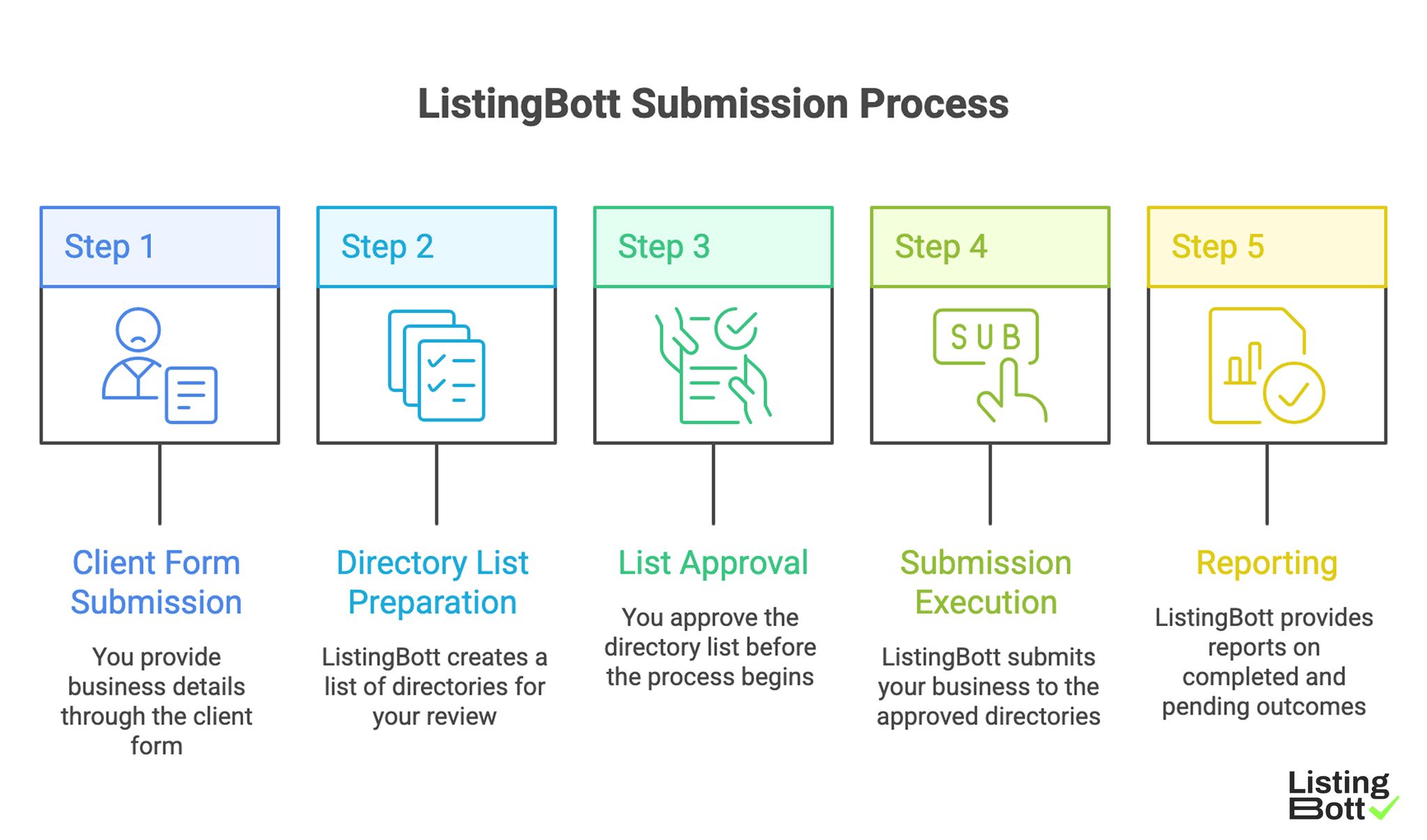
ListingBott Submission Process
-
You submit business details through the
client form. -
ListingBott prepares a
list of directoriesfor scope review. - You approve the list before process start.
- ListingBott executes submissions according to approved scope.
- ListingBott provides reporting for completed and pending outcomes.
Key features and practical value
- Intake validation: reduces preventable profile-data errors.
- Pre-publish approval: aligns execution scope before launch.
- Workflow transparency: supports coordination and escalation.
- Report handoff: enables quality review before next expansion wave.
Teams that prioritize workflow reliability generally maintain stronger execution quality than teams focused only on output volume.
Expected outcomes and limits
Expected outcomes:
- structured submission execution,
- clearer operational visibility,
- repeatable process for additional rollout waves.
Limits to keep explicit:
- no guaranteed ranking position,
- no guaranteed traffic by a specific date,
- no guaranteed indexing speed,
- no guaranteed outcomes controlled by third-party platforms.
DR commitment is conditional only. A promise to reach DR 15 can apply when starting DR is below 15, the client explicitly selects domain growth, and the directory list is approved before execution starts. Refunds may apply if process has not started, and current public language remains no hidden extra fees.
Risks/limits
Frequent Arizona rollout mistakes
- Expanding before capacity budget is defined.
- Running growth waves without approval-gate evidence.
- Ignoring reopen rate while tracking only new submissions.
- Allowing multiple data baselines across active lanes.
- Scaling while critical issue age is increasing.
Practical limits
- Directory submission supports discoverability and consistency, but does not replace broader SEO systems.
- Results and timing vary by category, competition, and third-party platform behavior.
- Fast expansion without capacity controls can create long-lived quality debt.
Minimum control layer
- lane-based expansion gates,
- SLA-bound correction ownership,
- weekly KPI review by lane,
- mandatory approval artifacts per expansion step.
FAQ
Why use a capacity-first model in Arizona?
Because execution quality depends on correction and governance capacity, not only submission output.
Should all coverage lanes launch at once?
Usually no. Launch by lane, stabilize metrics, then expand.
Which KPI should block expansion first?
Use critical-fix closure velocity with integrity pass rate by lane.
Can directory submission guarantee rankings?
No. It supports consistency and visibility, but rankings depend on external factors.
Is DR growth guaranteed for every project?
No. DR commitments are conditional and apply only to qualified setups.
What governance is required at minimum?
Canonical profile control, gate ownership, correction SLA, and recurring lane-level reporting.